Control system vulnerabilities put food & beverage at serious risk
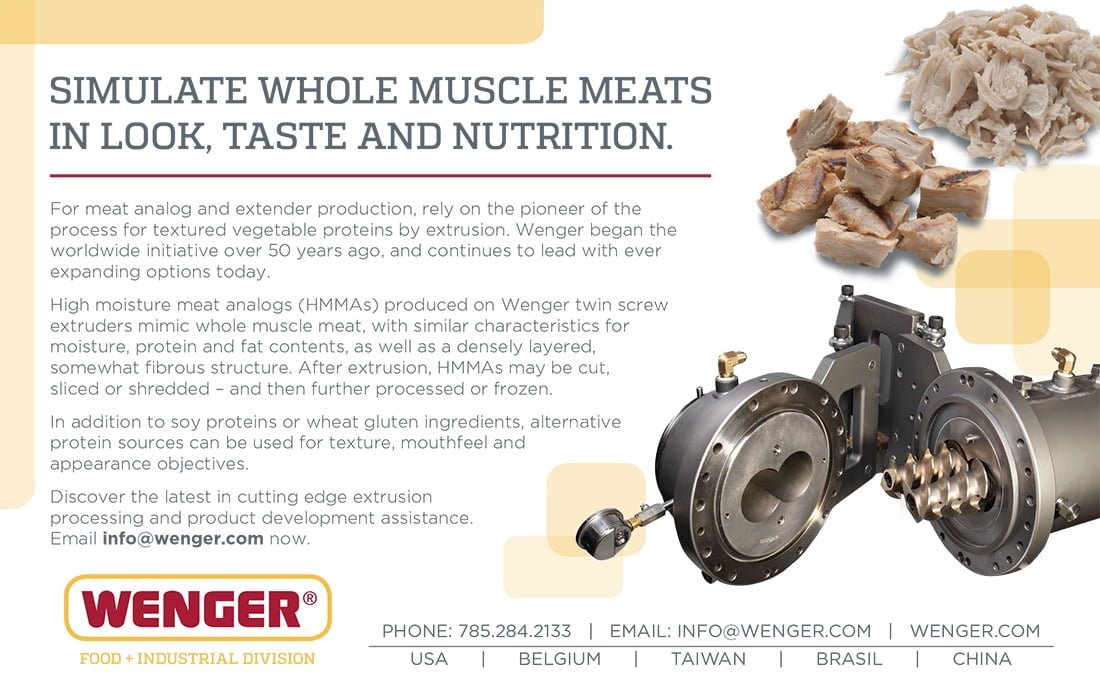
Out-of-control processes caused by an intruder can affect both food quality and safety.
Cybersecurity is often more critical at the industrial control level than the infrastructure level. Photo courtesy of Traitov via Getty Images
While cybersecurity risks may seem only within the purview of enterprise systems and critical infrastructure—such as the power grid, wastewater and transportation—the reality of it is that cybersecurity is often more critical at the industrial control system (ICS) level—and in the food and beverage industry, there are too many gaps in protection.
Unfortunately the number of vulnerabilities of sensitive ICS equipment isn’t improving. These vulnerabilities are largely caused either by “zero day” holes in vendor ICS equipment or the lack of an effective vendor software/firmware patch—or a patch that hasn’t been applied by the end user, a food or beverage processor or other manufacturer.
It’s one thing for a business system (e.g., ERP or inventory control) to be the victim of ransomware, but if attackers take over industrial control systems, the very safety of food can be threatened—for example, by undermining a kill step, changing ingredient additions or altering a cleaning system by hacking into the CIP/process control system.
While the vulnerability count for the food and agriculture industry is not at the same level as more critical manufacturing sectors, nevertheless, the significance is that out-of-control processes caused by an intruder can affect food quality and safety. Data source: Claroty Ltd.
Number of ICS vulnerabilities headed in the wrong direction
Throughout the second half (2H) of 2020, 71% of ICS vulnerabilities disclosed were remotely exploitable through network attack vectors, according to the second “Biannual ICS Risk & Vulnerability Report,” released by Claroty, an industrial cybersecurity company. The report also reveals a 25% increase in ICS vulnerabilities disclosed compared to 2019, as well as a 33% increase from the first half of 2020.
On the very day of writing this story, ICS CERT (Industrial Control Systems Cyber Emergency Response Team) released two ICS advisories for major automation suppliers. The first is for a controller with a buffer overflow vulnerability, and the second is for HMIs “missing authentication for a critical function” vulnerability.
The current Claroty Vulnerability Report discloses 449 vulnerabilities affecting ICS products from 59 vendors. Of these, 70% were assigned high or critical Common Vulnerability Scoring System (CVSS) scores, and 76% do not require authentication for an intruder to exploit the system.
While we have extolled the virtues of the convergence of IT and OT networks, the problem is that this integration increases the attack surface available to adversaries, says Amir Preminger, Claroty VP of research. “Nation-state actors are clearly looking at many aspects of the network perimeter to exploit, and cybercriminals are also focusing specifically on ICS processes, which emphasizes the need for security technologies such as network-based detection and secure remote access in industrial environments. It is heartening to see a growing interest in ICS within the security research community, as we must shine a brighter light on these vulnerabilities in order to keep threats at arm’s length.”
Food and beverage is not exempt from attacks
Obviously, critical manufacturing, energy, water and wastewater and commercial facilities sectors—all designated as critical infrastructure—were the most affected by vulnerabilities disclosed in the 2H report. For example, the critical manufacturing sector saw 194 reported vulnerabilities; energy, 186; water and wastewater, 111; commercial facilities, 108; and transportation, 70. But, next in the running was food and agriculture with 70 vulnerabilities reported in the sector. See the above chart, “Vulnerability count by infrastructure sector.”
Opportunistic attackers went especially “low” throughout 2020, elevating extortion and ransomware attacks within their arsenals and targeting these critical industries including food. This dynamic created a race between attackers, researchers and defenders to find exploitable vulnerabilities, especially in industrial control/SCADA systems and operational technology (OT) protocols and networks.
"It is heartening to see a growing interest in ICS within the security research community, as we must shine a brighter light on these vulnerabilities in order to keep threats at arm’s length.”
Why are the numbers up?
The number of ICS vulnerabilities disclosed in 2020 increased by nearly 33% compared to 2018 and almost 25% compared to 2019. The primary factors for the increase, says the report, are likely heightened awareness of the risks posed by these vulnerabilities and increased focus from researchers and vendors identifying and remediating such vulnerabilities as effectively and efficiently as possible. This growth also indicates security research focused on ICS products maturing.
There were nearly 61% of vulnerabilities discovered by third-party companies making them the most dominant research group. Among all third-party companies, there were 22 that reported their first disclosures, further evidence of growth in the ICS vulnerability research market.
Turning vulnerabilities into exploits
While IT/OT integrated manufacturing networks are great for monitoring and improving processes, they’re also a perfect entryway for attackers. The Claroty report found that 72% of ICS vulnerabilities are exploited through a network attack vector (that is, they are remotely exploitable). Nearly half (46.32%) of vulnerabilities found affect the basic control (Level 1) and supervisory control (Level 2) levels of the Purdue Model of network hierarchy or configuration (see “The Purdue Reference Model" (simplified) below).
IT
Level 5 Archives/file servers/enterprise network
Level 4 ERP/finance/messaging
Manufacturing zones: Device to Operations
Level 3 Operations management/historians —
Level 2 Supervisory controls: HMI, OI, client programs
Level 1 Controls: PLCs, RTUs, PACs, safety Ins. systems
Level 0 Sensors, actuators, drives, robots, etc.
Purdue Reference Model (simplified)
The Purdue Reference Model was originally developed by Theodore J. Williams with members of the Purdue University Consortium for computer integrated manufacturing. This greatly simplified diagram shows the basic manufacturing OT levels (0-3) and the IT levels at 4 and 5. Data flow can be upwards from the bottom or downwards from the top. However, for companies that wish to control OT equipment from the upper layers, care should be taken such that a minimal number of people have credentialed access to layers 0-3 from layer 4 or 5. Additional hardware protection and multiple factor logins should be required. Source: FE
Almost 15% of vulnerabilities found affect multiple types of products (operating at various OT Purdue Model levels, IIoT and network devices). This category mostly contains vulnerabilities in third-party components. Real scary is this: 89.98% of vulnerabilities don’t require special conditions to exploit, and an attacker can expect repeatable success every time.
Adding to the scary factor is that in 76.39% of the vulnerabilities, the attacker is unauthenticated prior to attack and doesn’t require any access or privileges to the target’s setting or files. In other words, the hacker is free to come and go at any time. In 78.17% of the vulnerabilities, there is no requirement for user interaction. And, 78.92% of the vulnerabilities that require no user interaction are remotely exploitable.
According to the report, for 81% of the supervisory control vulnerabilities, user interaction is needed if exploiting via a local attack vector. This indicates a playground for social engineering attack vectors. If exploited successfully, 66% of the vulnerabilities can cause total loss of system availability.
For 94.43% of the vulnerabilities, the impact to confidentiality is low or none, and for 80.4% of vulnerabilities the impact to integrity is zero. This demonstrates that while integrity and confidentiality of information is important in IT security, it is a lesser risk variable in OT networks, requiring further severity assessment of each vulnerability.
The top five most prevalent Common Weakness Enumerations (CWEs), manifested in the ICS vulnerabilities disclosed during 2H 2020, are all ranked highly on The MITRE Corporation’s 2020 CWE Top 25 Most Dangerous Software Weaknesses list, due to their relative ease of exploitation and high potential impacts.
As for adversaries, while there wasn’t a Triton-scale malware attack in 2020, threats continue to surface from nation-state actors and cybercriminals (the inclusion of ICS processes in the SNAKE ransomware kill list). Breaching the corporate perimeter is the first hop on the Purdue Model toward reaching the OT/controls layer; and while network defenses may be enhanced, incidents such as the SolarWinds attack demonstrate the fragility of some perimeter-based defenses and the eventuality that these attacks will land on ICS and SCADA equipment.
For more on the 2020 2H “Biannual ICS Risk & Vulnerability Report,” visit Claroty’s website.